Configure SAML with Keycloak¶
This page explains how to integrate Keycloak as a SAML Identity Provider to authenticate your users on Reemo.
Note
Configure SAML in Reemo¶
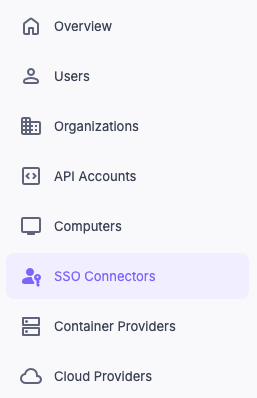
Access Connectors in the instance Admin Area.¶
Configure SAML in Organization > Connectors.¶
Create the SAML connector in Reemo¶
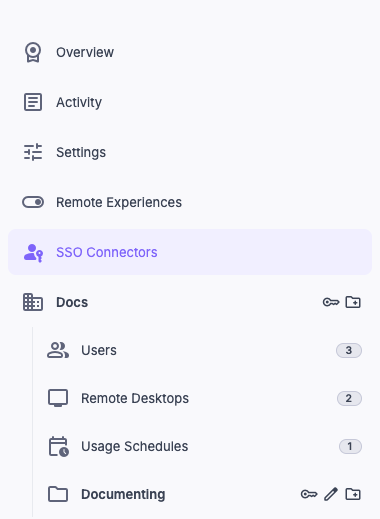
Create a new Connector of type SAML Connector.
Fill in the basic fields:
Friendly Name: name displayed to your users (e.g. Keycloak).
Issuer / App URI ID:
reemo.The other fields (e.g. Entry Point, Certificate) will be filled in after the Keycloak configuration.
Fill in the basic fields of the SAML connector.¶
Enter the friendly name and the Issuer (reemo), then save.¶
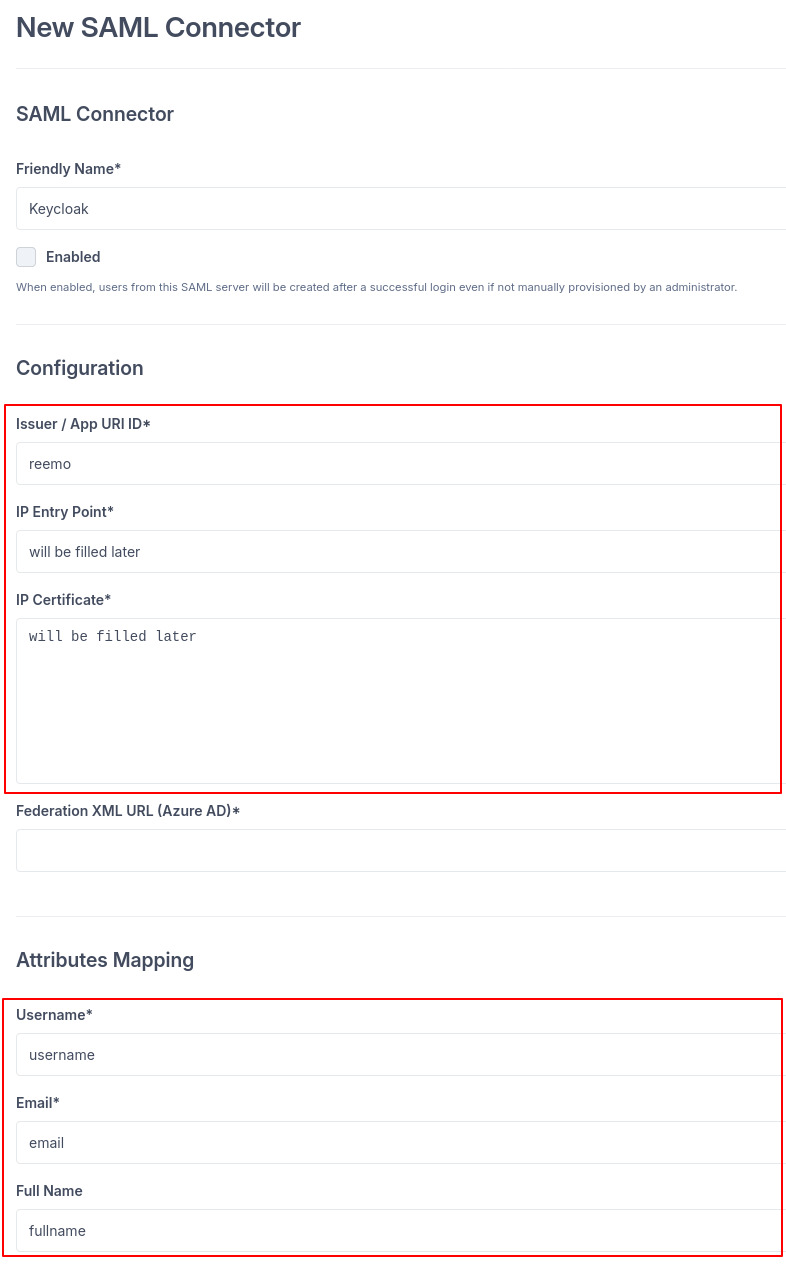
Validate to generate the connector’s callback URL. You will need it in Keycloak.
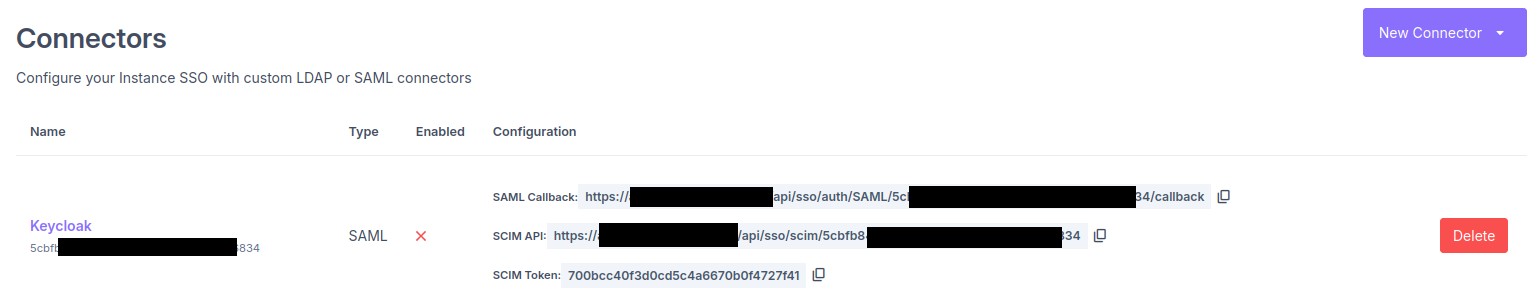
Copy the callback URL generated by the SAML connector.¶
Configure the SAML client in Keycloak¶
Log in to your Keycloak Admin Console.
Select the target Realm from the dropdown in the top left.
In the left menu, go to Clients > Create client.
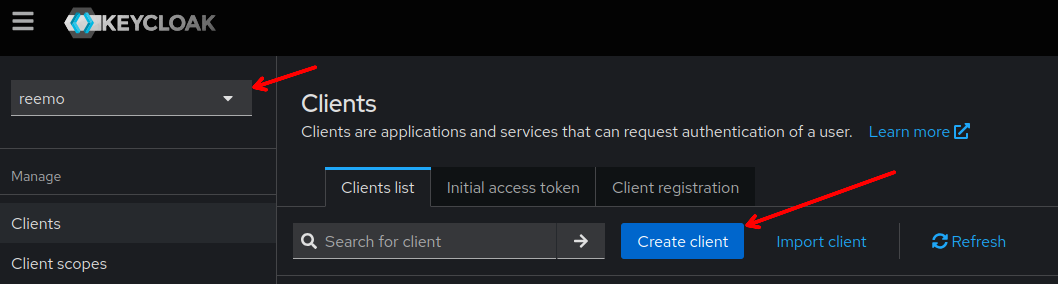
Create a new SAML client in Keycloak.¶
Fill in the client parameters:
Client type: SAML.
Client ID:
reemo.
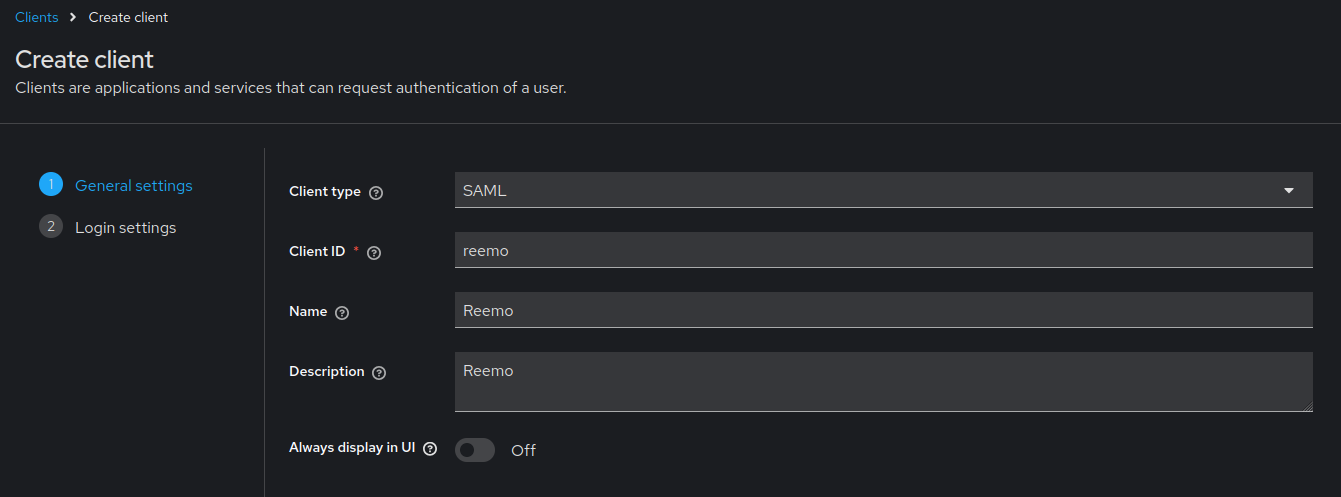
Set the client type and Client ID.¶
In the client settings, configure:
Valid redirect URIs: paste the callback URL from the Reemo connector.
Master SAML Processing URL: paste the callback URL from the Reemo connector.
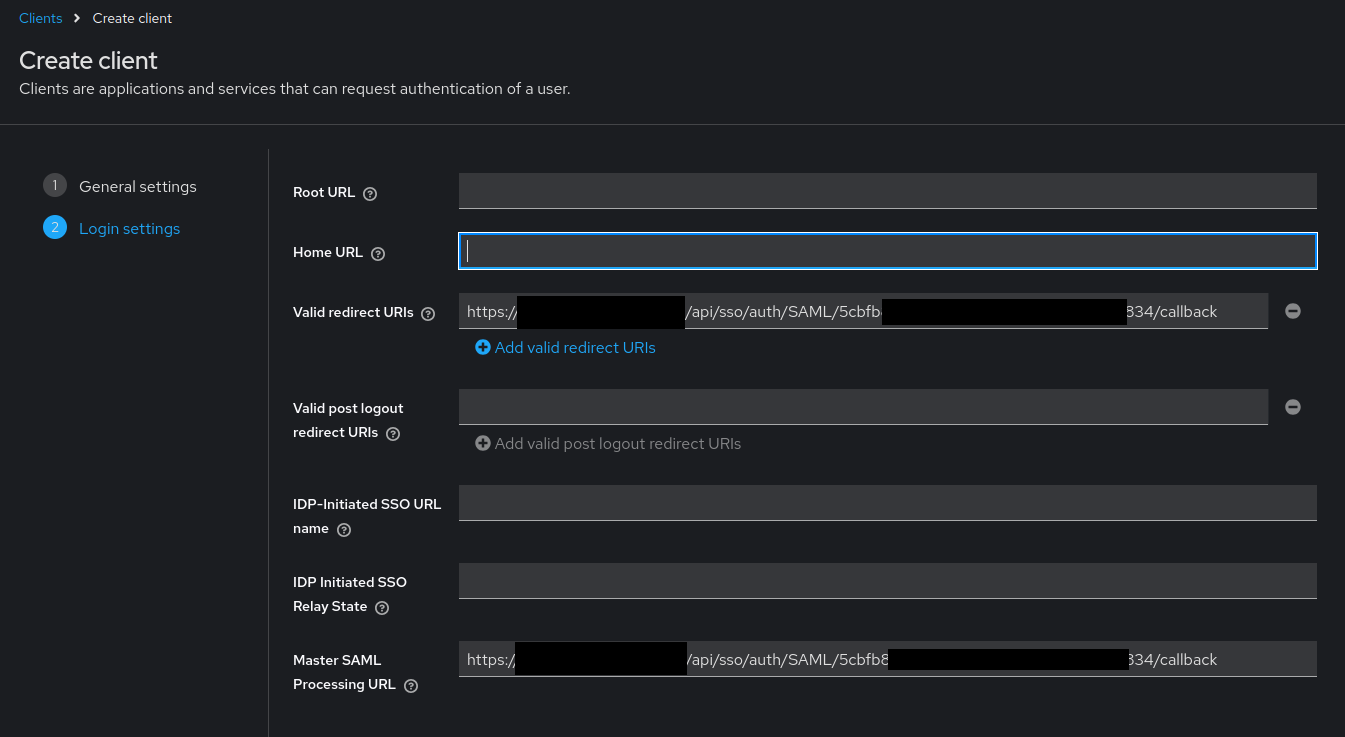
Fill in the redirect URIs and the Master SAML Processing URL.¶
Sign documents: ON.
Sign assertions: ON.
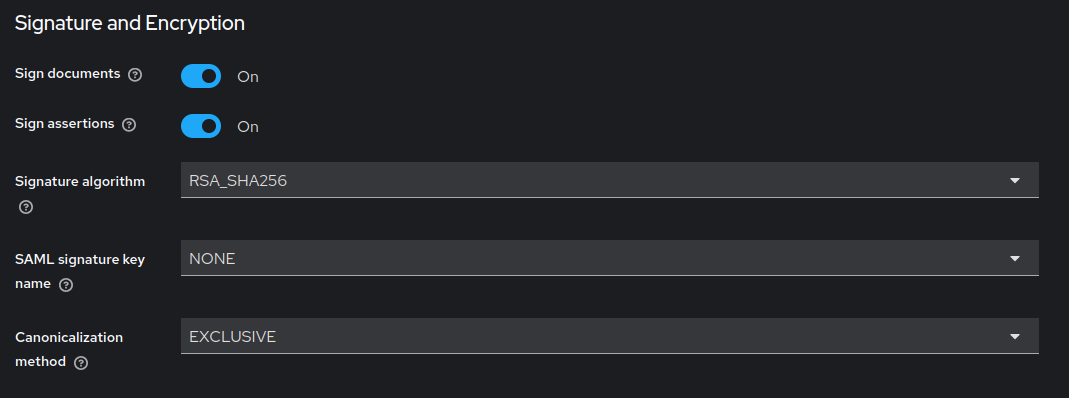
Enable Sign documents and Sign assertions.¶
Go to the client’s Keys tab and disable the Client signature required option.
Warning
Reemo does not sign outgoing SAML requests. If Client signature required remains enabled, Keycloak will reject authentication requests.
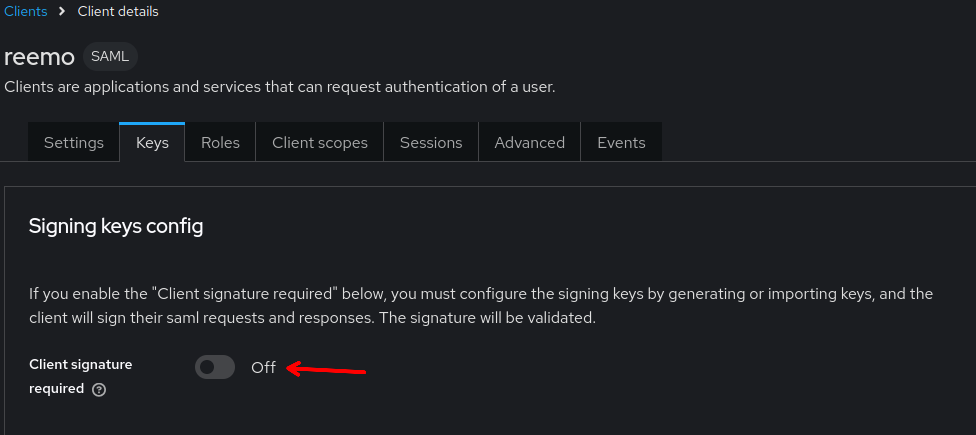
Disable Client signature required in the client Keys tab.¶
Go to the Client scopes tab > click on the dedicated scope (e.g.
reemo-dedicated) > Add mapper > By configuration.Add the following attribute mappers:
Mapper type
Name
Property
SAML Attribute Name
User Property
username
usernameusername
User Property
email
emailemail
User Attribute
fullname
fullnamefullname
Warning
The SAML Attribute Name field is mandatory on each mapper. Without it, attributes arrive anonymous in the SAML response and Reemo rejects them.
Warning
Keycloak does not natively concatenate first name and last name. You must create a custom fullname attribute on each user in the Keycloak console.
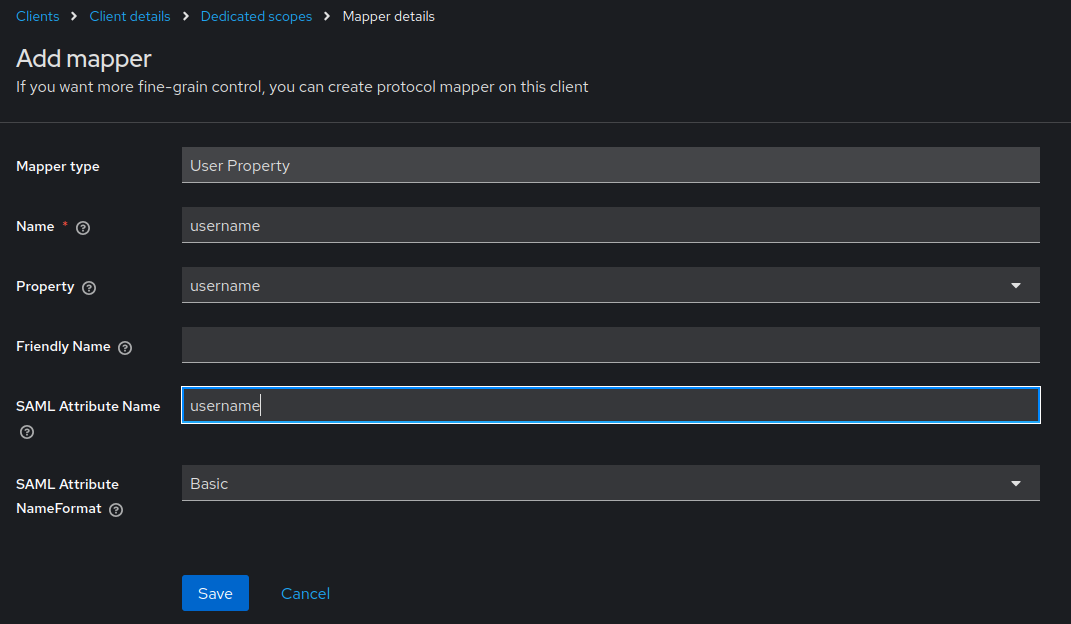
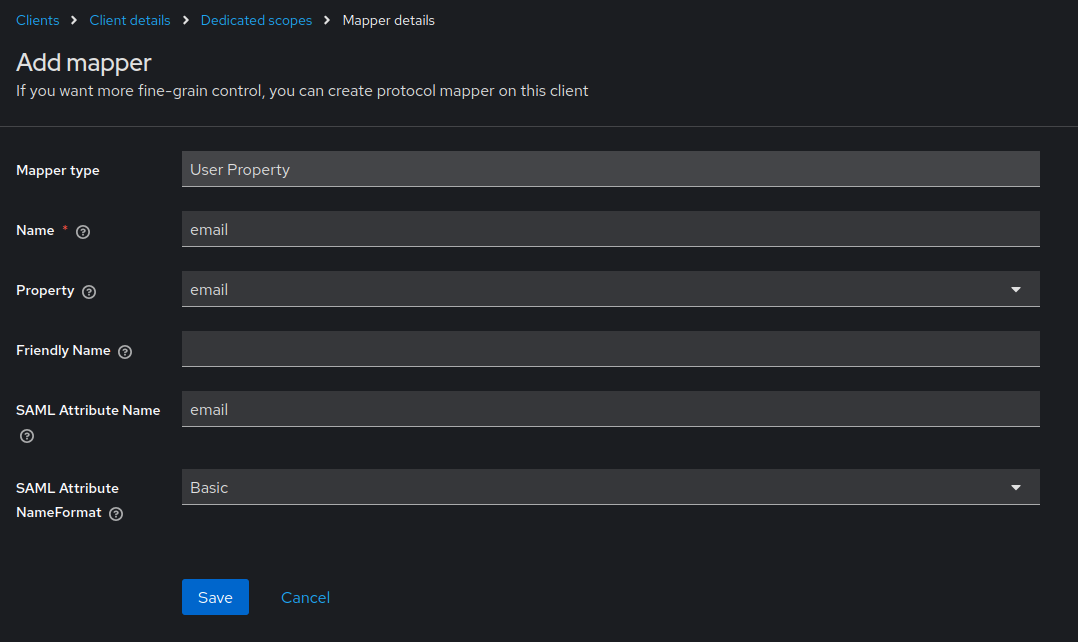
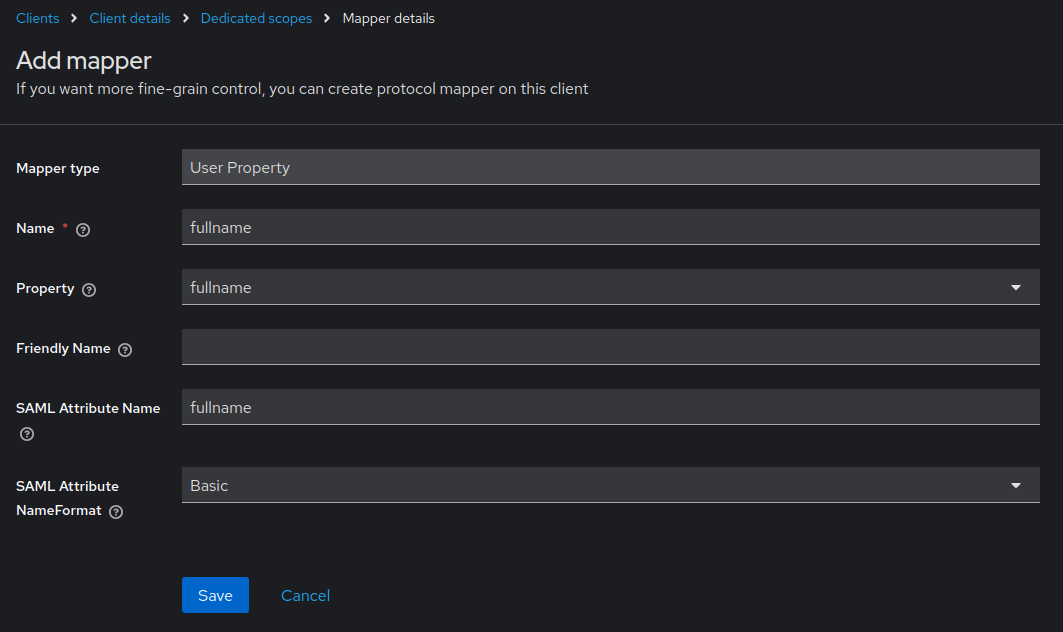
Configure the email, username and fullname mappers in Client scopes.¶
Retrieve the X.509 certificate and the Entry Point (SSO URL):
Certificate: from Realm settings > Keys > RS256 row > Certificate button. Copy the raw base64 content.
Entry Point: follows the format:
https://[keycloak_url]/realms/[realm]/protocol/saml
Warning
Use the RS256 certificate from the Realm, not from the client. Paste only the raw base64 without headers, otherwise Reemo will not be able to validate the signed assertions.
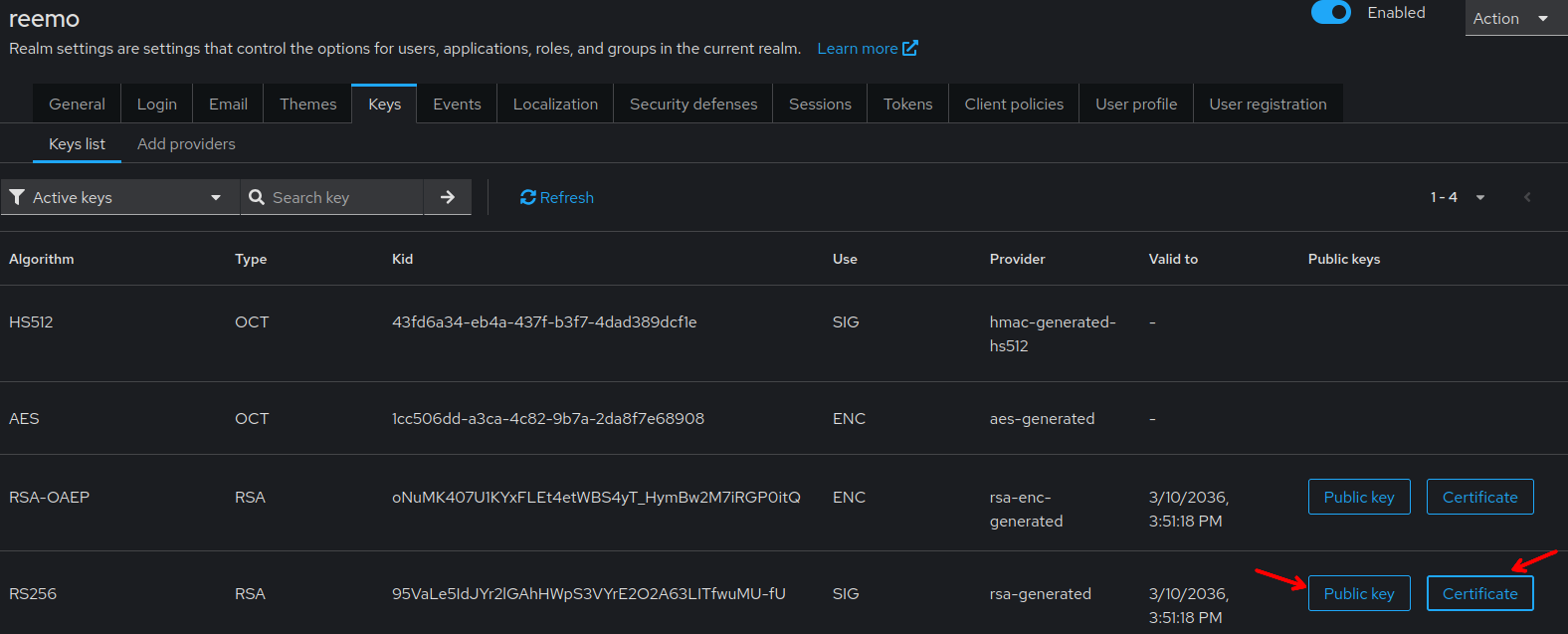
Retrieve the RS256 Realm certificate from Realm settings > Keys.¶
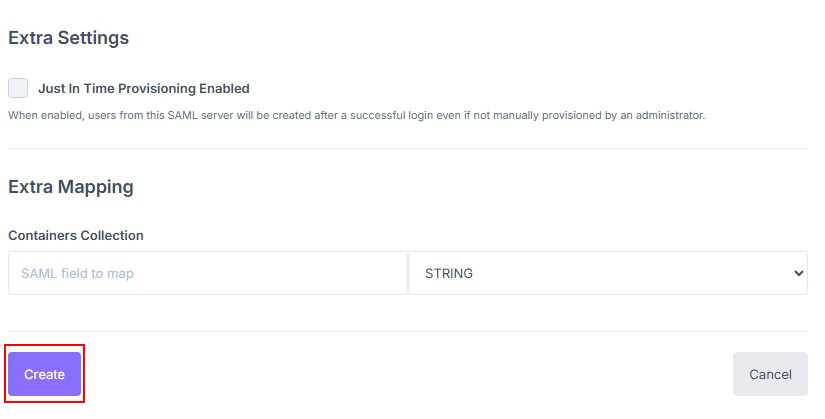
Complete the Reemo SAML connector with this information. Enable the connector (check Enabled) then click Update to save.
Declare users¶
Two approaches are available to grant SSO access to users.
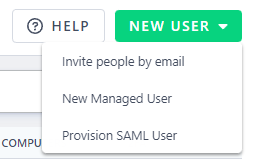
Provision SAML users directly in the organization.¶
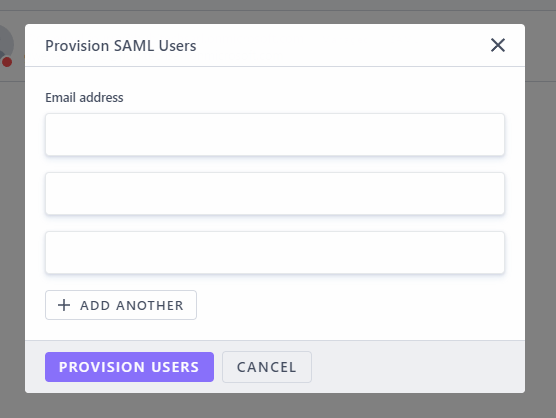
Add users by email via the provisioning popup.¶
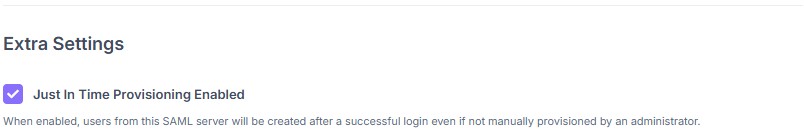
Enable Just In Time Provisioning to create accounts on first login.¶
Log in via SAML¶
Once the connector is active and users are declared (or JIT is enabled), your users can log in:
General access to your portal (Private Cloud / On-Prem):
https://[portal_url]/
Direct access to the organization (Public Cloud):
https://[portal_url]/login/[organization_shortname]
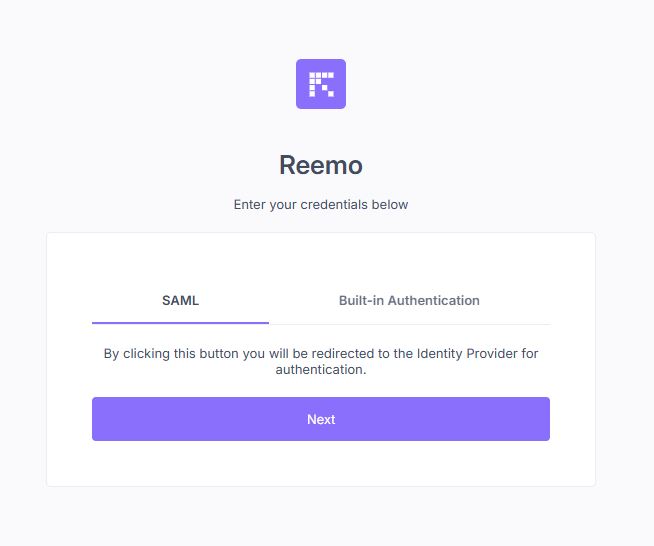
Select SAML then Next to be redirected to Keycloak.¶